DMARC: Unlocking Email Security with Domain-based Message Authentication, Reporting & Conformance
Email spoofing is a serious threat to businesses of all sizes. By sending emails that appear to be from a legitimate sender, attackers can trick recipients into clicking on malicious links, opening infected attachments, or providing sensitive information.
What is DMARC?
DMARC works by adding a TXT record to your domain's DNS. This record contains instructions for how the recipient email servers should handle emails that fail DMARC authentication.
DMARC is a powerful tool that can help to protect your business from email spoofing. DMARC stands for Domain-based Message Authentication, Reporting and Conformance. It is an email authentication protocol on a DNS level that helps to verify the authenticity of emails sent on behalf of your domain.
In the digital age, email has become an integral part of our lives, both personally and professionally. However, it has also become a primary target for cybercriminals seeking to exploit vulnerabilities through email phishing attacks. To combat this growing threat, organizations and individuals need robust email authentication protocols like DMARC (Domain-based Message Authentication, Reporting, and Conformance). In this blog post, we will delve into the importance of DMARC and uncover key facts about email phishing that underline the necessity of implementing effective protection measures.
The Prevalence of Email Phishing:
Email phishing has become a pervasive and sophisticated technique used by cybercriminals to trick recipients into divulging sensitive information or taking malicious actions. It often involves deceptive emails designed to appear legitimate, such as masquerading as trusted organizations or individuals. According to industry reports, phishing attacks continue to rise, with billions of malicious emails sent daily.
Financial and Reputational Risks:
Email phishing poses significant financial and reputational risks for individuals and businesses. Successful phishing attacks can result in financial losses, including unauthorized access to bank accounts, theft of personal or business data, or fraudulent transactions. Moreover, falling victim to a phishing attack can damage an organization's reputation, eroding customer trust and confidence.
Email Authentication Trio: SPF, DKIM, and DMARC:
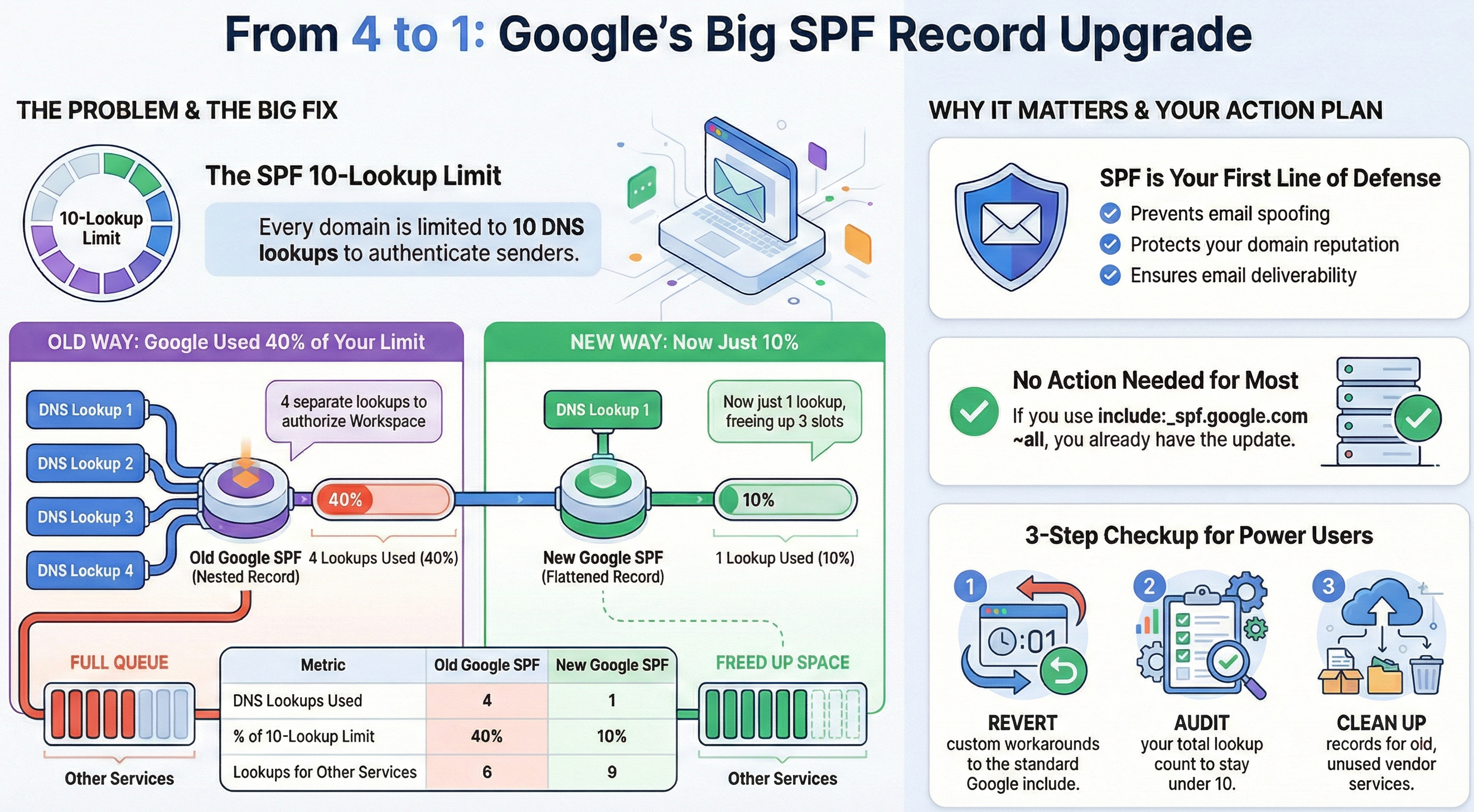
DMARC complements two existing email authentication protocols: SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail). SPF verifies the sender's IP address, ensuring it aligns with the domain's authorized sending sources. DKIM adds a digital signature to the email, confirming its integrity and origin. DMARC utilizes SPF and DKIM authentication results to determine email handling, allowing organizations to set policies that range from monitoring and reporting to outright blocking of suspicious messages.
Enhanced Visibility and Control:
One of the significant advantages of DMARC is its reporting capabilities. DMARC provides detailed feedback and visibility into the email ecosystem, including information about failed authentication attempts and potential sources of abuse. This valuable data allows organizations to identify vulnerabilities, detect and mitigate phishing threats effectively, and fine-tune their email security strategy.
Collaboration and Industry Standards:
DMARC promotes collaboration within the email ecosystem. By implementing DMARC, organizations demonstrate their commitment to email security, encouraging ISPs (Internet Service Providers) and email receivers to respect DMARC policies and protect their email domains. Furthermore, industry standards are emerging that require DMARC implementation, making it a vital component in securing email communications.
How to Implement DMARC
To implement DMARC, you will need to create a TXT record in your domain's DNS. This record will tell email servers how you want to handle emails that fail SPF or DKIM verification.
There are three different DMARC policies that you can choose from:
- p=none: This policy tells email servers to do nothing with emails that fail SPF and/or DKIM verification.
- p=quarantine: This policy tells email servers to quarantine emails that fail SPF and/or DKIM verification.
- p=reject: This policy tells email servers to reject emails that fail SPF and/or DKIM verification.
Example DMARC XML report
You can use a DMARC generator to help you create a record that is specific to your domain.
You can sign up for a free 14 days trial with DMARCIAN DMARC monitoring account that will collect DMARC generated XML reports and convert into a human readable graphical interface.
DMARCIAN detail viewer example:
Here is an example of DMARC capable email sources
Here is an example of Threat/unknown sources
DMARC reports will tell you how many emails are failing SPF or DKIM verification, and how email servers are handling those emails. This information can help you to improve your DMARC policy and make your email domain more secure.
Conclusion:
In the face of escalating email phishing threats, DMARC has emerged as a crucial line of defense for individuals and organizations. By implementing DMARC alongside SPF and DKIM, you can significantly reduce the risk of falling victim to phishing attacks, safeguard your sensitive information, and preserve your brand reputation. Remember, protecting your email domain is not just about your own security; it's about contributing to a safer and more trustworthy email ecosystem for everyone.